Restricting Public-Facing Azure Storage Accounts Using Azure Resource Policy
Background
Back in September 2017, Microsoft has announced Virtual Network Service Endpoints for Azure Storage and Azure SQL at Ignite. This feature prevents Storage Accounts and Azure SQL Databases from being accessed from the public Internet.
A customer had a requirement to enforce all storage accounts to be attached to VNets as part of their security policies. The Azure Resource Policy seems to be the logical solution for this requirement. In order to make this possible, I have contacted the Azure Policy product team, and thanks for their prompt response, this is now possible – although at the time of writing, it is yet to be documented on the Microsoft documentation site. Therefore, I’m here sharing the policy definition and my experience on this blog post.
Policy Definition
{
"if": {
"allOf": [
{
"field": "type",
"equals": "Microsoft.Storage/storageAccounts"
},
{
"field": "Microsoft.Storage/storageAccounts/networkAcls.defaultAction",
"equals": "Allow"
}
]
},
"then": {
"effect": "deny"
}
}
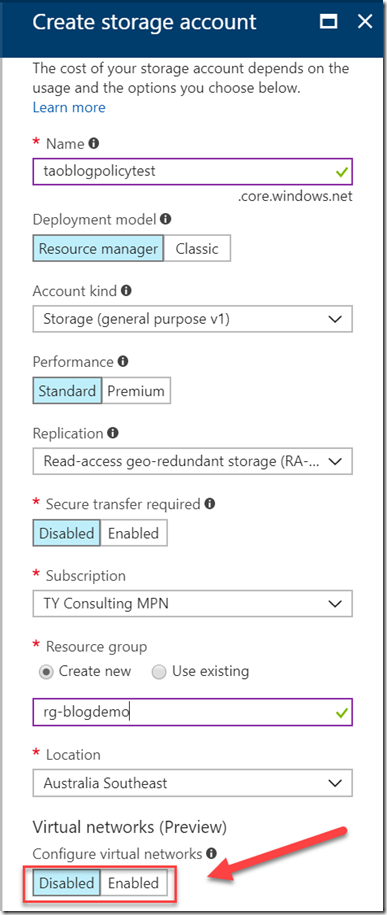
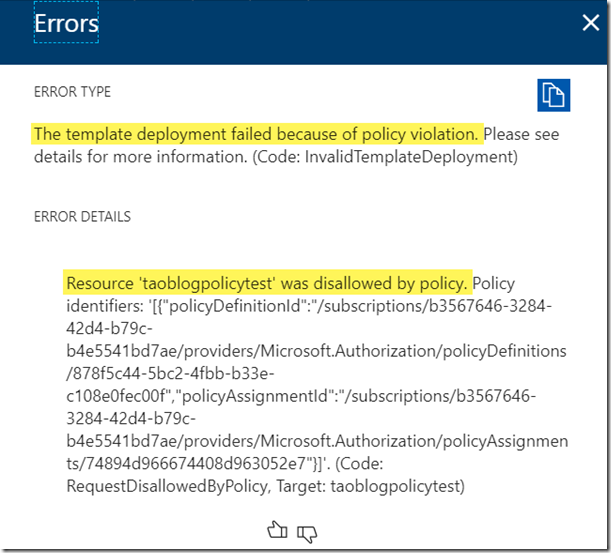
Once the policy is applied, you will not be able to create a Storage Account without attaching to a VNet:
Limitations
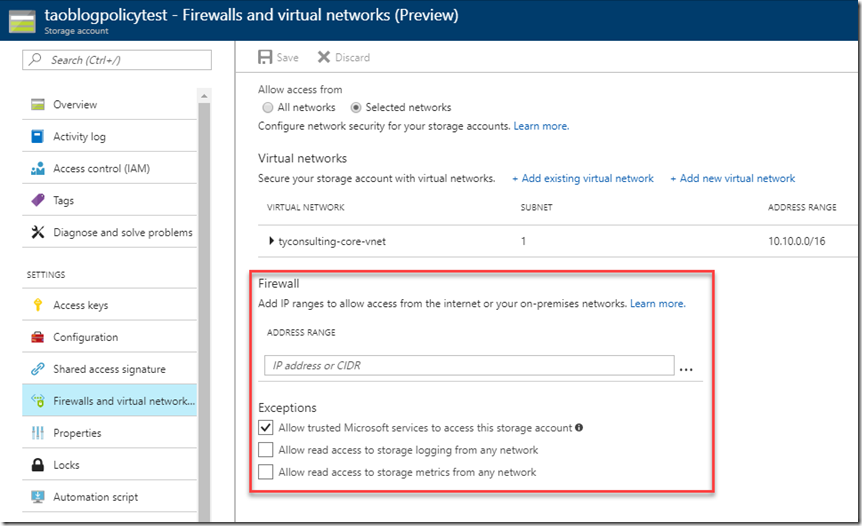
Even when you have attached the Storage Account to a VNet, the Network Security Group (NSG) that the VNet is associated to does not apply to the storage account. This is because, according to Microsoft’s documentation, NSG only applies to subnet, classic VMs and NICs attached to ARM VMs. For Storage Accounts, if you need to access it from an external network, you will need to configure the firewall rules for each storage account individually:
According to my own tests, at the time of writing this post, the firewall rules for storage accounts cannot be configured and enforced via Azure Resource Policy.
[Update: 21/09/2018]: to configure the firewall rules, please refer to my post: https://blog.tyang.org/2018/09/21/azure-policy-to-restrict-storage-account-firewall-rules/


Leave a comment