How To Configure OpsMgr 2012 Web Console Single Sign-On
I was trying to configure single sign-on for the OpsMgr 2012 Web Consoles so dashboard users don’t need to enter credentials on shared display screens. I spent almost a day trying to make it work until I gave up and called Microsoft Premier Support yesterday.
On all my management groups, web consoles are installed on a dedicated servers. All the web consoles are connecting to the management servers Load Balancing (NLB) address for Data Access Service rather than individual management servers.
Long story short, since I couldn’t manage to find a clear instruction / requirements for OpsMgr 2012 Web Console single sign-on, the steps listed below is what I had to take to make this work with the help from Microsoft CSS.
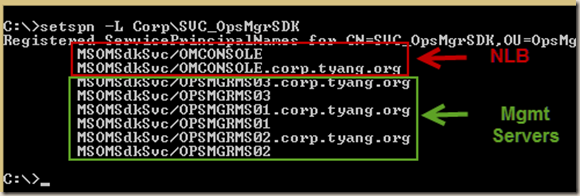
1. Data Access Service (SDK) SPN’s
Make sure the SPN’s for the management servers Data Access Service is correctly configured. SPN’s are also required for the NLB addresses:
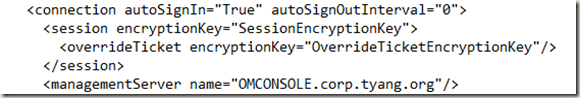
2. Web Console config file Web.Config
In <OpsMgr 2012 R2 Install Dir>\WebConsole\WebHost\Web.config, the connection tag is configured as below:
<connection autoSignIn=”True” autoSignOutInterval=”0”> <session encryptionKey=”SessionEncryptionKey”> <overrideTicket encryptionKey=”OverrideTicketEncryptionKey”/> </session> <managementServer name=”<Mgmt Server or NLB Address>”/> </connection>
i.e.
Note: I also configured autoSignOutInterval=”0” so the web console doesn’t time out.
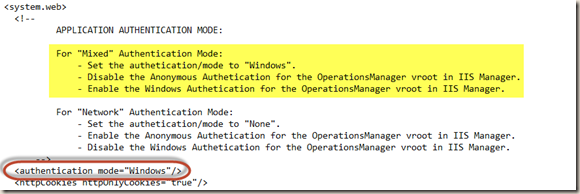
further down in the web.config file, make sure authentication mode is set to “Windows”
<authentication mode=”Windows” />
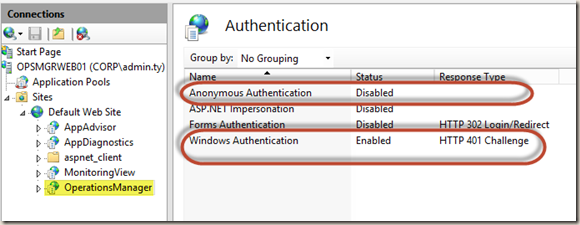
Note: According to the note shown above, the Anonymous authentication should be disabled and Windows Authentication should be enabled for the OperationsManager vroot in IIS
3. Constraint Delegation on the Web Console computer account
While I was trying to make it work before calling Microsoft, I followed the guide from this blog article: Running the Web Console Server on a standalone server using Windows Authentication. Although it was written for OpsMgr 2007, constraint delegation is still required.
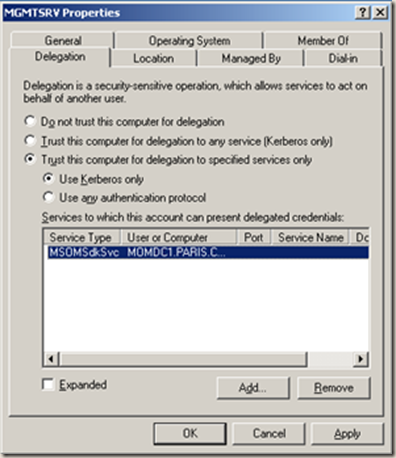
I added the MSOMSdkSvc service for all management servers to the list as instructed on the last page of this document:
Above screenshot was taken from the guide. However, it turned out it doesn’t seem like the guide is 100% correct for OpsMgr 2012 (I can’t confirm for 2007 as I don’t have a 2007 management group in my lab anymore).
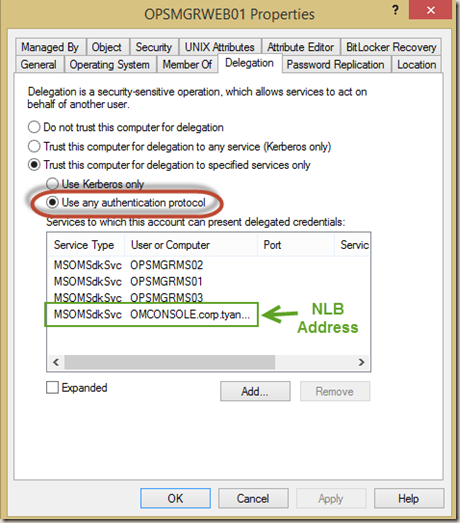
Instead of choosing “Use Kerberos Only”, we should choose the other option “Use any authentication protocol”. This is where I got stuck as before I called Microsoft, I did change the NLB address to a management server in the web.config but it didn’t make a difference. Otherwise it would have worked then.
I also had to add the NLB address to the list because my web console is configured to use NLB:
This is all that’s required for Single Sign On. After I reboot the web console server, I managed to open the console without getting prompted for credentials.
Disclaimer: this article is purely based on my own experience. I managed to configure single sign-on on 4 OpsMgr 2012 R2 management groups at work and 1 at home. Please don’t hold me accountable for any issues you may have in your environment.

Leave a comment