Using Postman Invoking Azure Resource Management APIs
 When working with REST APIs, Postman (https://getpostman.com) is a popular tool that needs no further introductions. This week, I’ve been pretty busy working on the upcoming Inside OMS V2 book, and I’m currently focusing on the various OMS REST APIs for the Custom Solutions chapter. I want to use Postman to test and demonstrate how to use the OMS REST APIs. Since most of the ARM based APIs requires oAuth token in the authorization header, I needed to configure Postman to contact Microsoft Graph API in order to generate the token for the API calls.
When working with REST APIs, Postman (https://getpostman.com) is a popular tool that needs no further introductions. This week, I’ve been pretty busy working on the upcoming Inside OMS V2 book, and I’m currently focusing on the various OMS REST APIs for the Custom Solutions chapter. I want to use Postman to test and demonstrate how to use the OMS REST APIs. Since most of the ARM based APIs requires oAuth token in the authorization header, I needed to configure Postman to contact Microsoft Graph API in order to generate the token for the API calls.
Initially, I thought this would be very straightforward and should have been done by other people in the past. I did find several posts via my favourite search engine, which were good enough to get me started, but I was not able to find one that explains how to configure Postman to request for the token natively without using external processes to generate the token. Therefore, I’m going to document what I have done here so I can reference this post in the Inside OMS book ![]() .
.
Note: I’m using the Windows desktop version of Postman, the UI may be slightly different than the Chrome extension version.
Step 1: Create an Azure AD application and service principal for Postman.
I have automated the creation process using a PowerShell script shown below:
#Requires -Modules AzureRM.Resources, AzureRM.Profile
#Modify below variables
$SubscriptionName = "Tao Playground"
$ApplicationDisplayName = "Postman"
#region functions
Function New-Passowrd
{
[CmdletBinding()]
PARAM (
[Parameter(Mandatory = $true)][int]$Length,
[Parameter(Mandatory = $true)][int]$NumberOfSpecialCharacters
)
Add-Type -AssemblyName System.Web
[Web.Security.Membership]::GeneratePassword($Length,$NumberOfSpecialCharacters)
}
#endregion
#region main
#Variables
$SignOnUrl = "https://www.getpostman.com"
$ReplyUrl = "https://www.getpostman.com/oauth2/callback" #Do not change this one
Write-Output "Loging to Azure"
Add-AzureRMAccount
#Add-AzureRMAccount -Credential $AADCred
$Context = Set-AzureRmContext -SubscriptionName $SubscriptionName
$SubscriptionId = $Context.Subscription.SubscriptionId
$TenantId = $Context.Tenant.TenantId
$ApplicationPassword = New-Passowrd -Length 16 -NumberOfSpecialCharacters 0
$Application = New-AzureRmADApplication -DisplayName $ApplicationDisplayName -HomePage $SignOnUrl -IdentifierUris "http://$ApplicationDisplayName" -ReplyUrls $ReplyUrl -Password $ApplicationPassword
Write-OUtput "Creating Azure AD Application Service Principal."
$ApplicationServicePrincipal = New-AzureRmADServicePrincipal -ApplicationId $Application.ApplicationId
Write-Output "Assigning the Contributor role to the application Service Principal..."
$NewRole = $null
$Retries = 0
While ($NewRole -eq $null -and $Retries -le 5)
{
# Sleep here for a few seconds to allow the service principal application to become active (should only take a couple of seconds normally)
Start-Sleep -Seconds 10
New-AzureRmRoleAssignment -RoleDefinitionName Contributor -ServicePrincipalName $Application.ApplicationId -ErrorAction SilentlyContinue
Start-Sleep -Seconds 10
$NewRole = Get-AzureRmRoleAssignment -ServicePrincipalName $Application.ApplicationId -ErrorAction SilentlyContinue
$Retries++
}
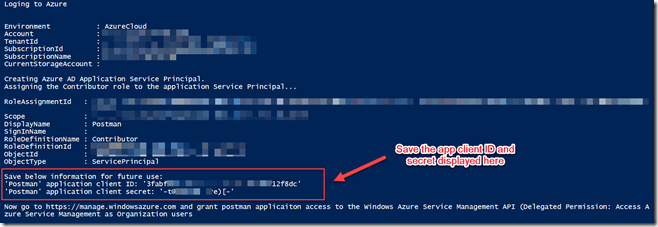
Write-Output "Save below information for future use:"
Write-Output "Azure Subscription Id: '$SubscriptionId'"
Write-Output "'$ApplicationDisplayName' application client ID: '$($Application.ApplicationId.ToString())'"
Write-Output "'$ApplicationDisplayName' application client secret: '$ApplicationPassword'"
Write-Output ""
Write-Output "Now go to https://manage.windowsazure.com and grant postman applicaiton access to the Windows Azure Service Management API (Delegated Permission: Access Azure Service Management as Organization users"
#endregion
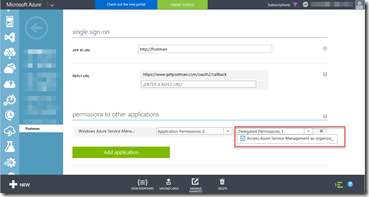
Step 2: Grant ‘Postman’ application permission to the Windows Azure Service Management API.
Note: steps demonstrated below MUST be completed in the Azure classical portal. Based on my experience, I was not able to give the Azure AD application permission to “Windows Azure Service Management API” from the new ARM portal.
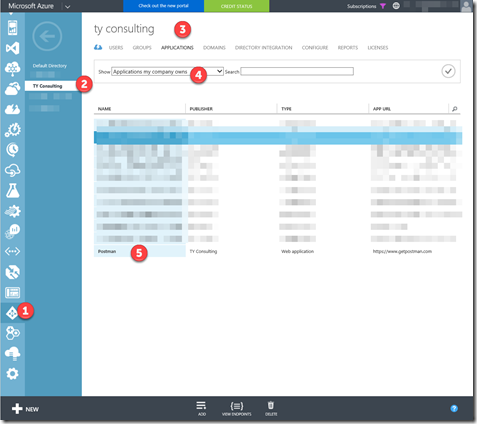
Once the ‘Postman’ Azure AD application is created, logon to the Azure classical portal (https://manage.windowsazure.com), browse to Azure AD, select the directory of where the application is created, then go to Applications, show “Applications my company owns”, locate the “Postman” application.
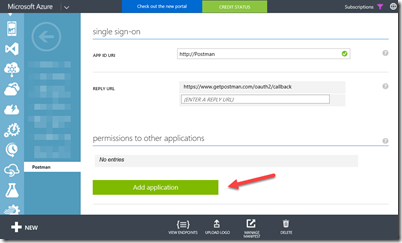
Click the “Postman” application, go to “Configure” tab, and click “Add Application”.
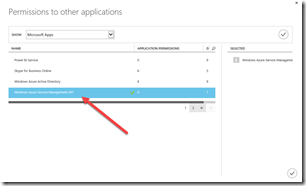
Add “Windows Azure Service Management API”
Tick “Access Azure Service Management as Organization users” under the “Delegated Permissions” drop down list and then click on “Save”.
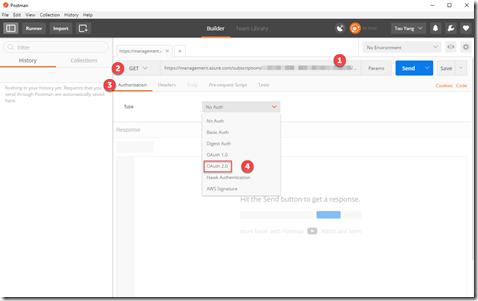
Step 3: Configure Authorization in Postman.
In Postman, enter an URI for an ARM REST API call, in this example, I’ll use the OMS REST API to retrieve a list of workspaces. Here’s the URI I’m using: https://management.azure.com/subscriptions/{subscription id}/providers/microsoft.operationalinsights/workspaces?api-version=2015-03-20
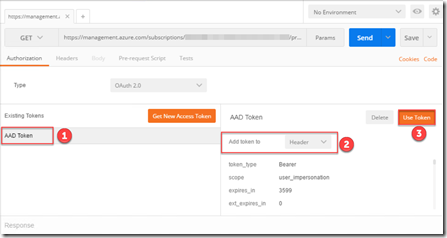
Make sure the HTTP method is set to “GET”, and then click on Authorization. For the “Type” drop down list, select OAuth 2.0
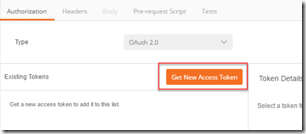
Click on “Get New Access Token”.
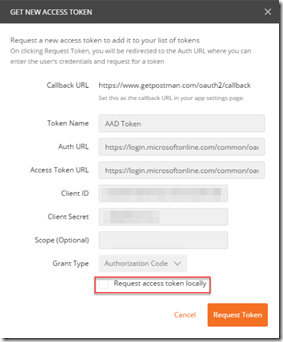
Enter the following information in the “Get New Access Token” popup window:
- Token Name: AAD Token
- Auth URL: https://login.microsoftonline.com/common/oauth2/authorize?resource=https%3A%2F%2Fmanagement.azure.com%2F
- Access Token URL: https://login.microsoftonline.com/common/oauth2/token
- Client ID: <output from the script in Step 1>
- Client Secret: <output from the script in Step 1>
- Grant Type: Authorization Code
- Make sure “Request access token locally” checkbox is unchecked.
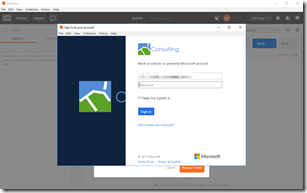
Click on “Request Token”, you will get the Azure AD sign-in page, enter the credential of an Organization account, – based on my experience, Microsoft accounts (i.e. @outlook.com) do not always work.
If everything goes as planned, you will see a new token been generated. you need to select the token, and add it to the request header:
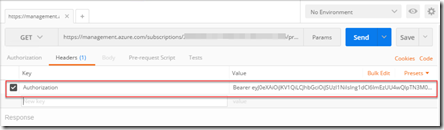
Now, go to the “Headers” tab, you should see the Authorization header:
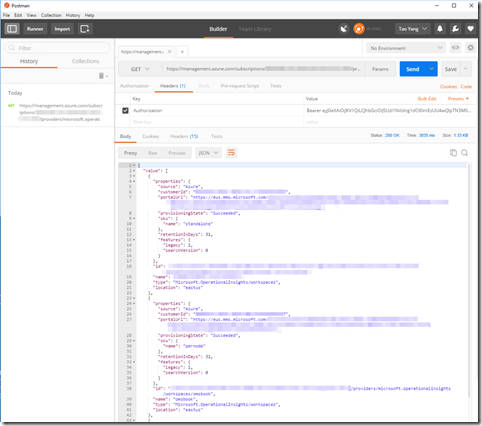
You may need to add additional headers for the request depending on the requirements of the API, but in this case, I don’t need any, I can just call the API by clicking on Send button.
Now I can see all my OMS workspaces in this particular subscription listed in the response body.
This concludes the work through, please do let me know if you are running into issues.
Lastly, This post has been a great help for me (although it’s for Dynamic CRM, not for Azure, it did point me to the right direction): https://blogs.msdn.microsoft.com/devkeydet/2016/03/22/using-postman-with-azure-ad/

Leave a comment