AzPolicyLens - Automated Azure Policy Insights and Reporting

Introduction
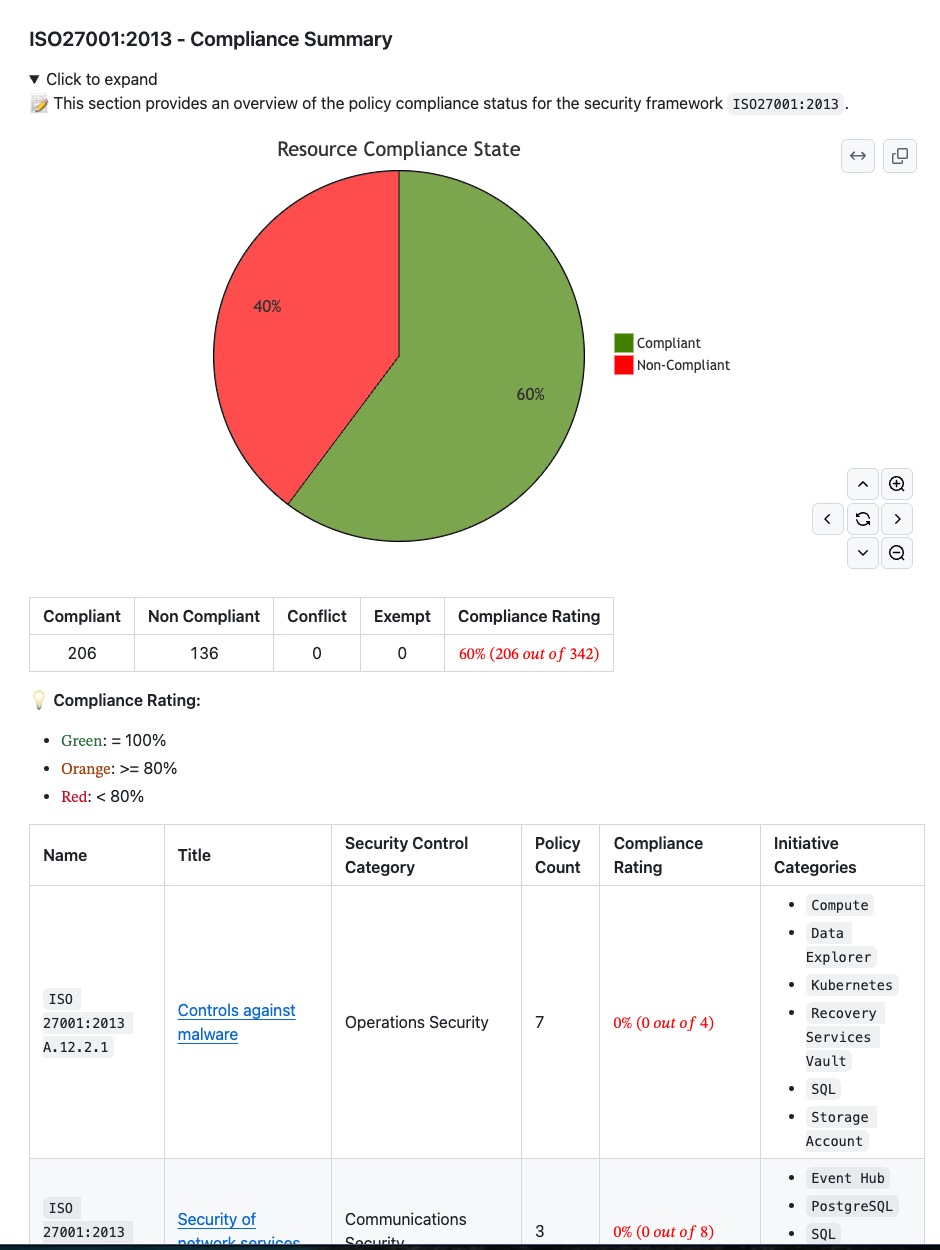
AzPolicyLens is a solution that automatically generates insights and reports based on Azure Policy data. It provides a comprehensive view of the policy compliance status across your Azure environment, helping you identify areas of non-compliance and take corrective actions.
This solution has been in active development for the last 12 months, and I am excited to share that I have finally released it to the public. You can find the project at aka.ms/AzPolicyLens.
In this blog post, I will provide an overview of AzPolicyLens, its features, and how it can benefit your organization.
12/05/2026 - Update: I have published a video introducing AzPolicyLens on AzureTar YouTube channel. You can watch the video below:
Problem Statement
While working in many customer environments over the last few years, I have observed the following challenges related to Azure Policy:
- Lack of visibility
- Lack of policy compliance reporting and monitoring
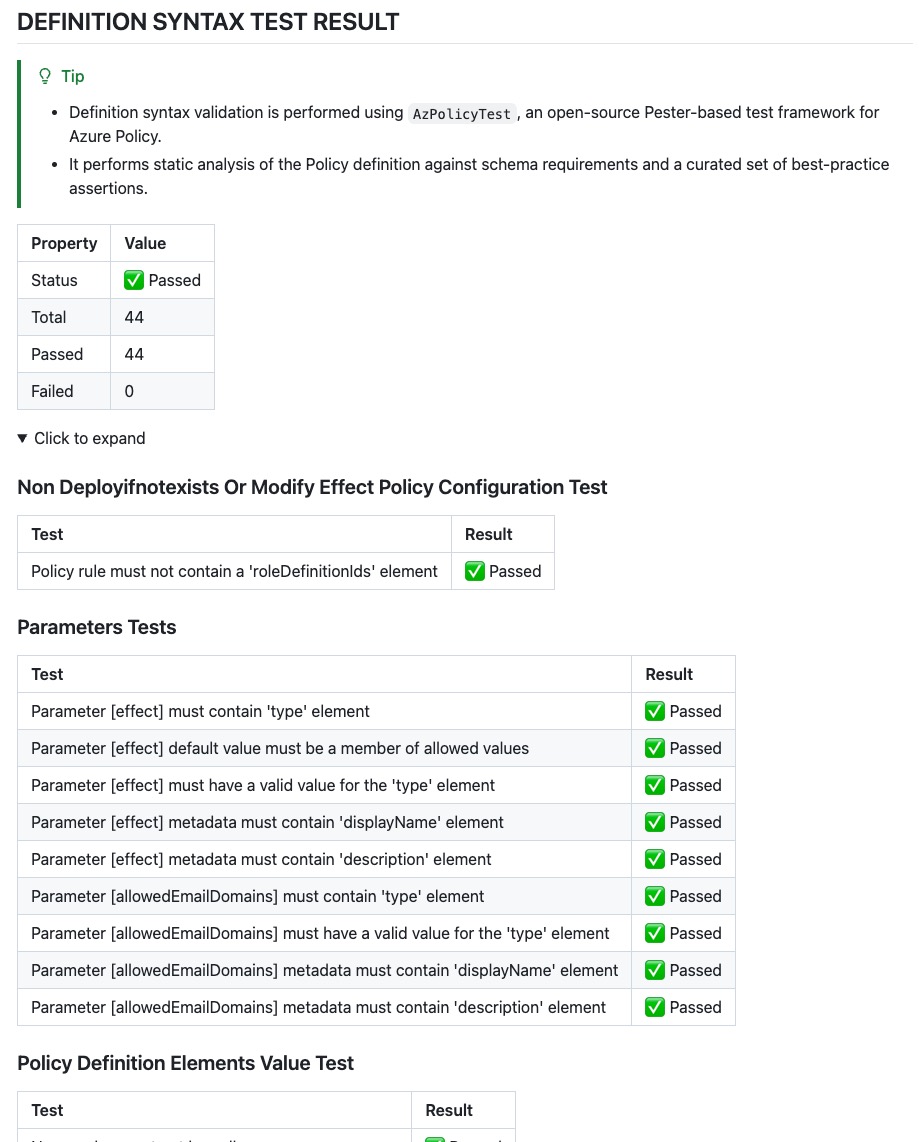
- Inconsistent, overlapping, incorrect policy definitions
- Lack of documentation for application teams, i.e.:
- How should we configure our Azure resources
- What is the service offering from the Azure landing zone?
- Lack of security control mapping
- Lack of compliance reporting dimensions
With these challenges in mind, I set out to create a solution that would address these issues and provide a comprehensive view of Azure Policy compliance across an organization.
Features of AzPolicyLens
AzPolicyLens is an automated solution that generates insights and reports based on Azure Policy data.
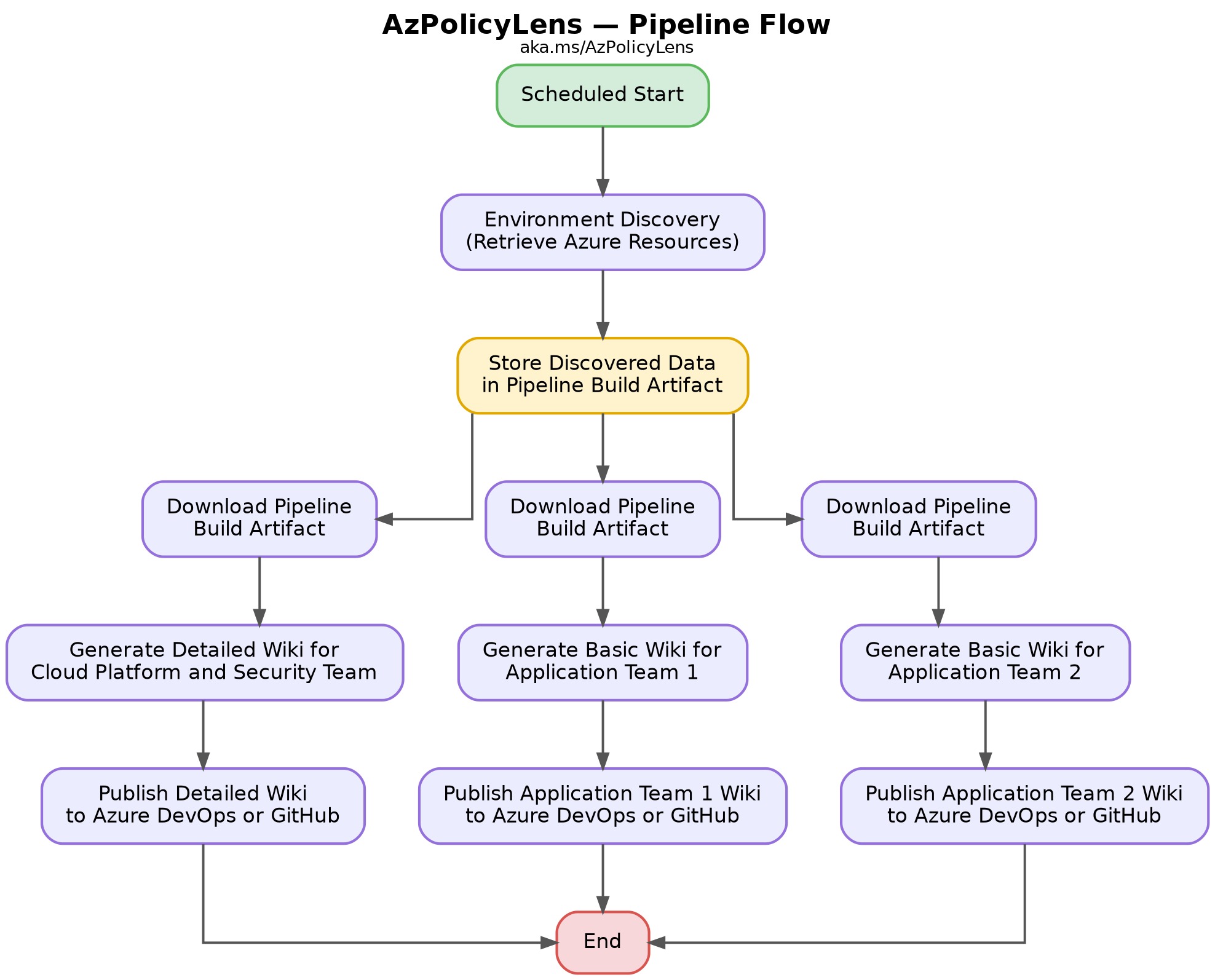
It supports the two most commonly used DevOps tools, Azure DevOps and GitHub. It provides an Azure DevOps pipeline and a GitHub Actions workflow to generate Markdown wiki content for both Azure DevOps code wiki and GitHub wiki.
The target audience for the generated wiki includes:
- Azure platform engineers and administrators
- Azure cloud architects
- Security Architects and Security Operations teams
- Application developers and architects
- Compliance and audit teams
Offering
The solution offers:
- Detailed wiki for cloud engineering and security teams
- Security control catalog for native built-in and custom controls
- Ability to integrate internal security controls into the wiki (treated the same as built-in security controls)
- Tailored wiki for each application team focusing on their own data
- Integration with existing CI/CD platforms (supports Azure DevOps and GitHub Actions)
The detailed features can be found in the Feature Comparison section of the solution documentation.
Image Gallery
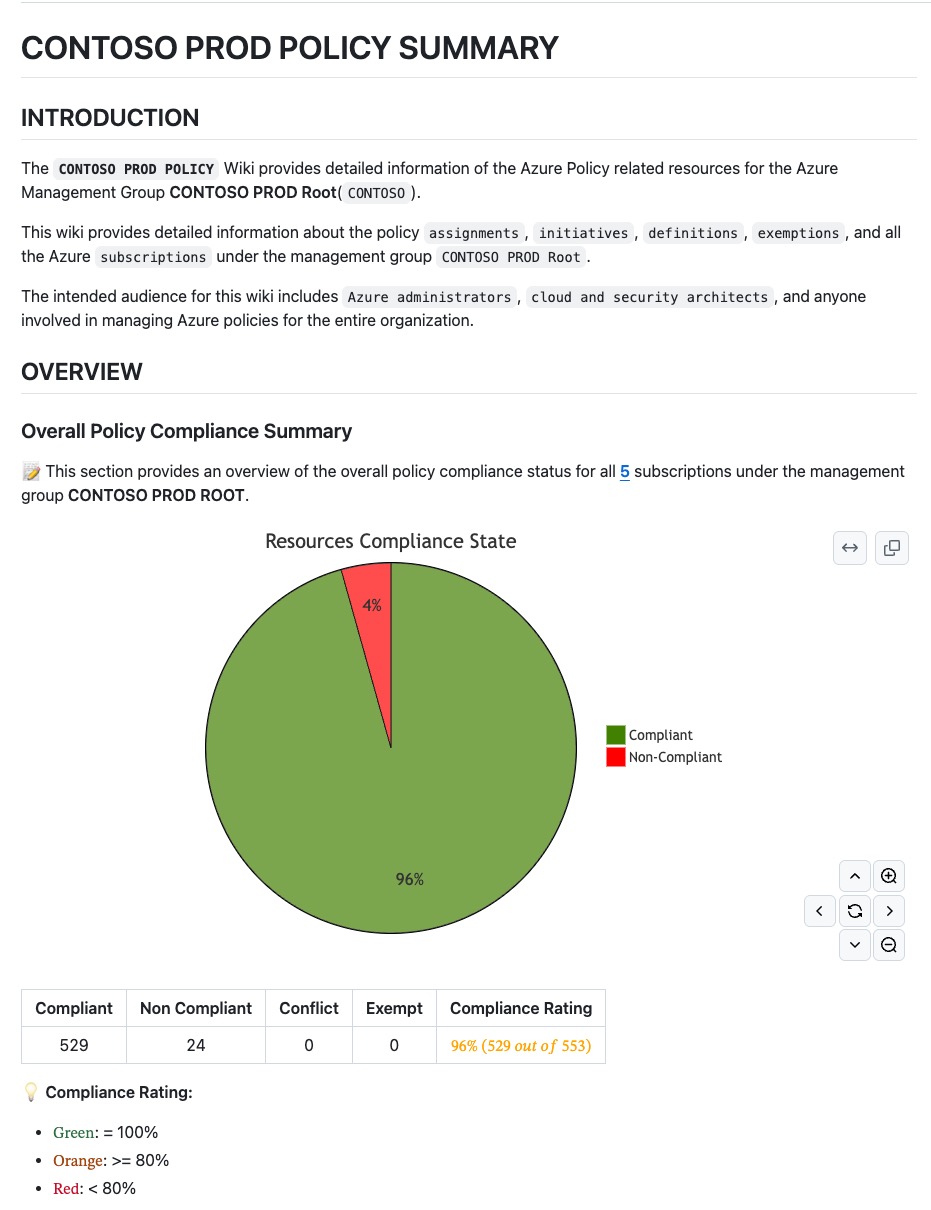
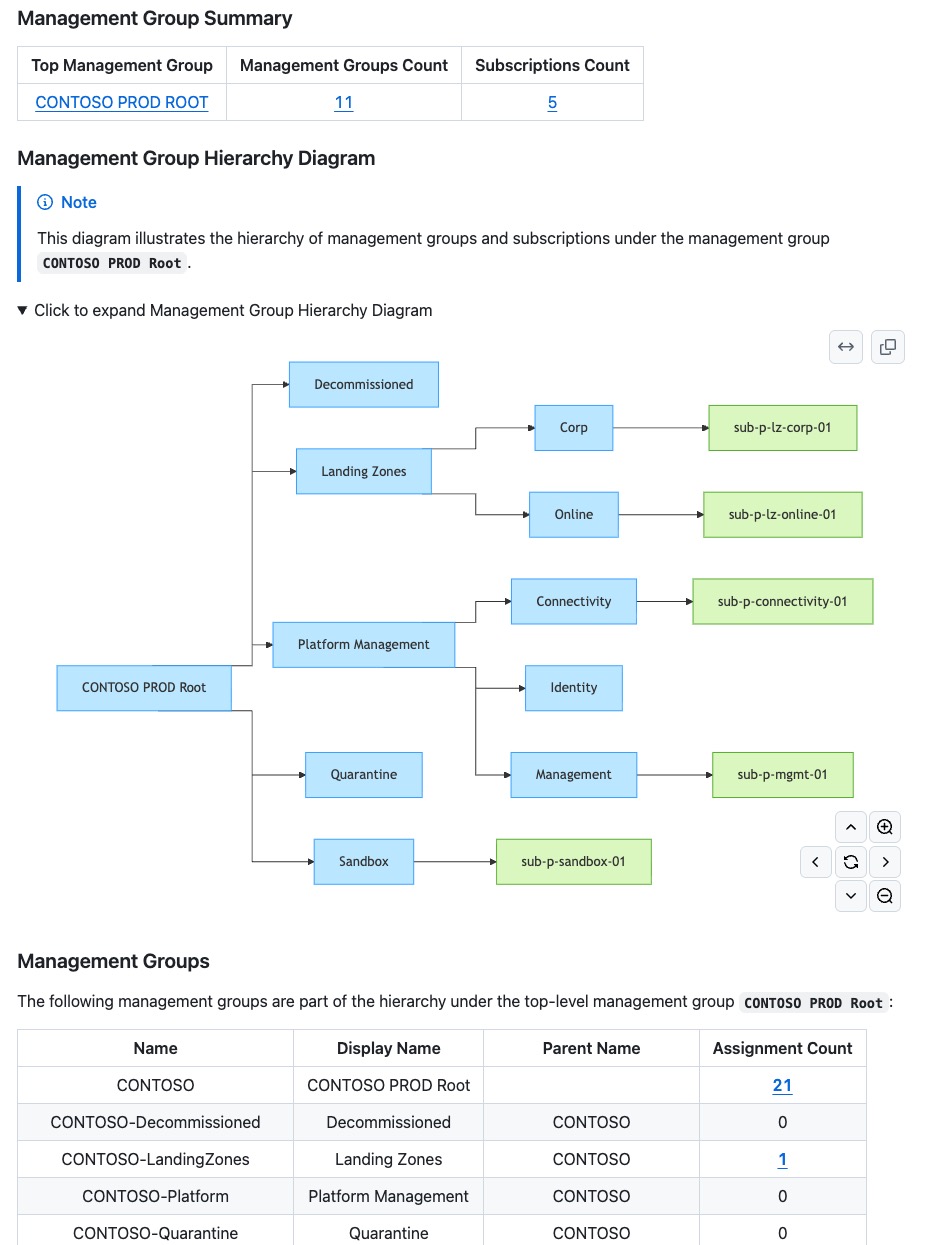
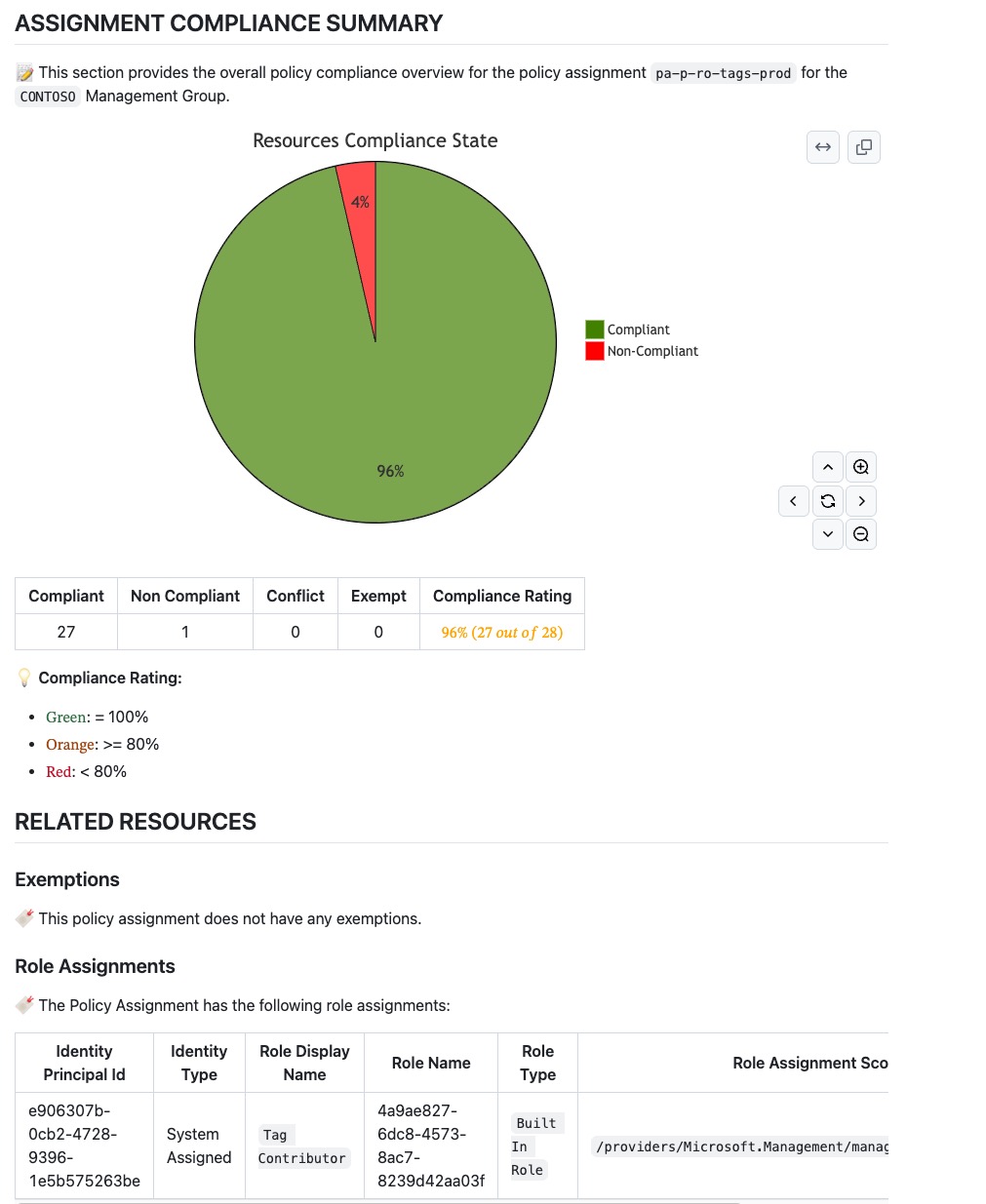
![]() Here are some screenshots (Click to enlarge) of the generated wiki content from AzPolicyLens (for comprehensive sample wiki sites, please refer to the demo wiki sites).
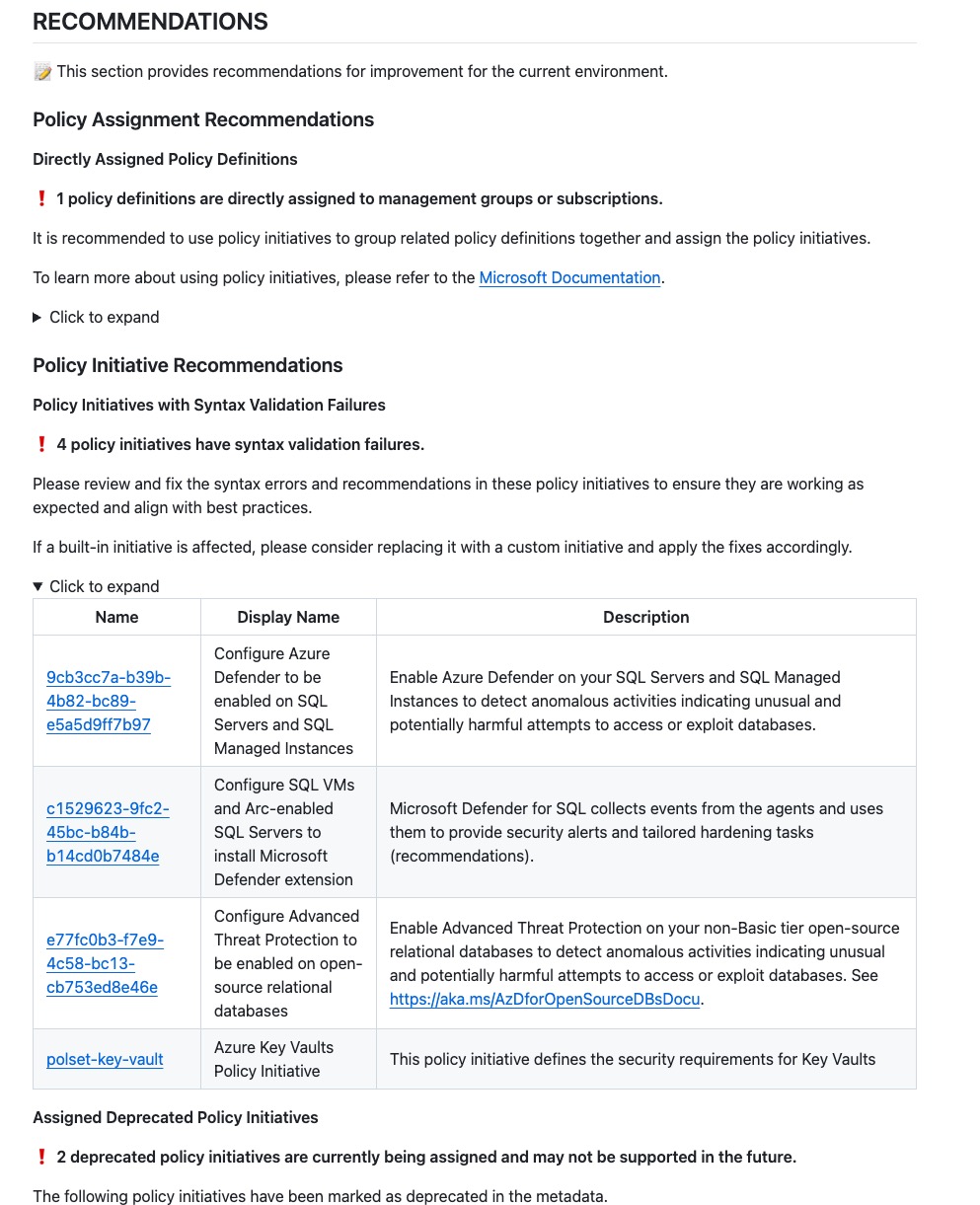
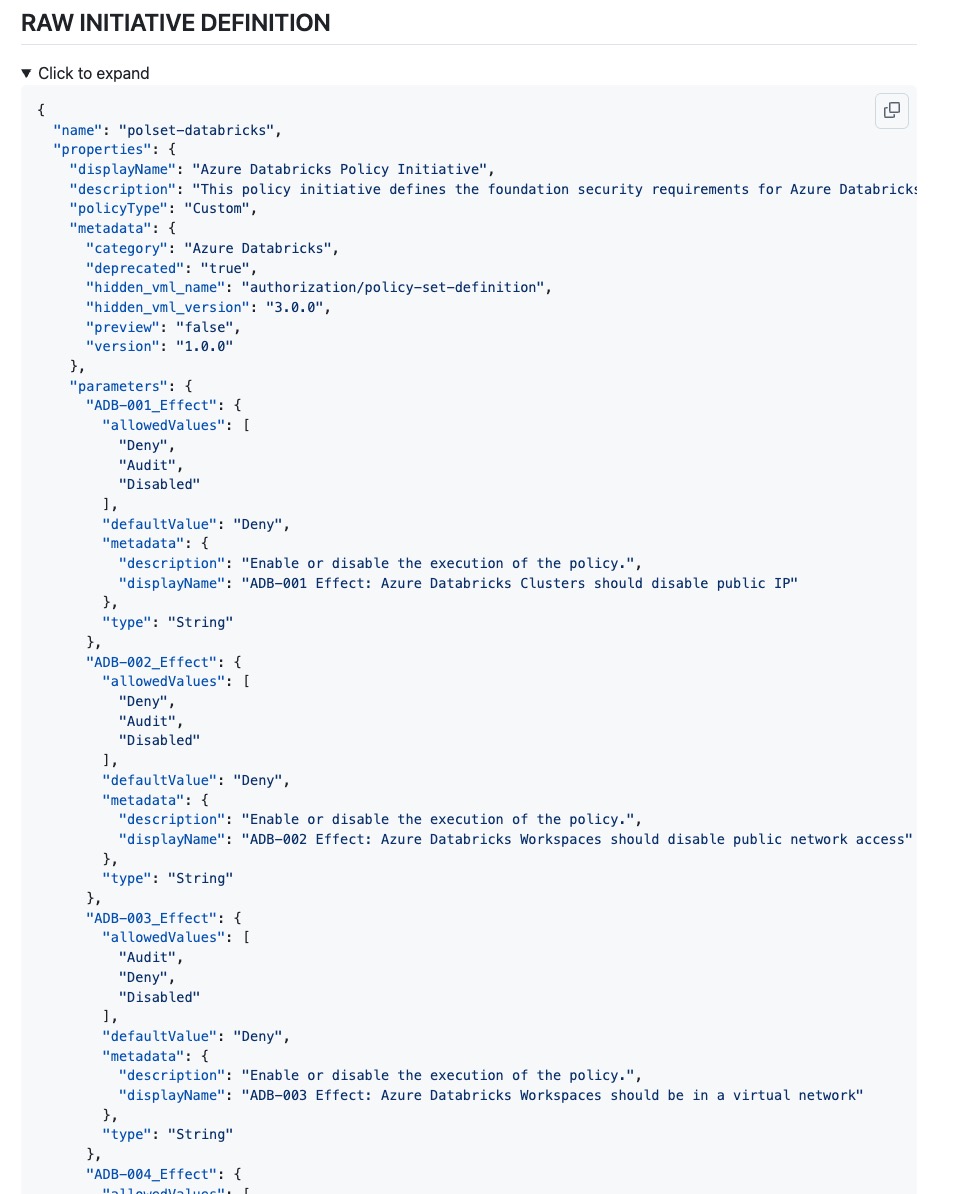
Here are some screenshots (Click to enlarge) of the generated wiki content from AzPolicyLens (for comprehensive sample wiki sites, please refer to the demo wiki sites).


Wiki Pipelines
The pipelines are designed to run either manually or on a schedule, with security in mind. No privileged roles are required to gather the data (only the Reader role is required in Azure). The pipelines perform a single discovery and use the same discovery data to generate one or more copies of the wiki for different personas and teams.
The discovery data does not contain any sensitive information and can be configured to be encrypted at rest with customer-managed keys.
Benefits
By using AzPolicyLens, organizations can gain the following benefits:
- Visibility into policy compliance and security posture
- Inclusion in the landing zone service offering for application teams (customers)
- Integration of in-house security controls with policy reporting
- A library of external and internal security frameworks and controls for reference and use in policy development
- Compliance reporting across multiple dimensions:
- In the overall specified scope
- By individual subscriptions
- By policy assignments
- By security frameworks
- By custom security controls
- By specific security controls
- By policy categories
- Insights into areas for improvement and actionable recommendations
- Assistance with ongoing policy development and maintenance
- For Azure cloud consultants and partner solution providers, this solution can be used as a tool for an initial assessment of a customer’s existing Azure environment, as well as ongoing monitoring and reporting.
Conclusion
Whether you are responsible for your organization’s Azure environment or you are an Azure consultant working with a customer’s Azure environment, I strongly recommend giving this solution a try, as I believe it solves many common challenges related to Azure Policy management and compliance reporting.
Credits
Over the last 12 months, from an initial prototype based on a customer’s request to a fully released solution, I have received a lot of feedback and suggestions from many people. I want to take this opportunity to thank everyone who has contributed to the development of this solution, including:
- Thanks to Pete Zerger and NingNing Zhao - my favourite CISSPs - for their valuable feedback and suggestions from the perspective of security practitioners at different levels, which was crucial in designing a solution that meets the needs of different personas in the security and compliance space.
- Thanks to Alex Verkinderen and Ahmad Abdalla for their feedback and suggestions from an Azure platform engineering perspective, which was crucial in designing a solution that meets the needs of Azure platform engineers and architects.
- Thanks to Johan Dahlbom, Alessandro Cardoso, Andreas Washita, Sebastian Gräf, and many other colleagues within Microsoft for the guidance and encouragement that helped me navigate the internal process of releasing this as an open-source solution under the Microsoft banner.
- Thanks to the project team from the customer (whom I cannot name here) for the initial request and for the time and support to develop the first prototype in the customer’s environment, which became the foundation of this solution.
- Lastly, thanks to Ahmad and Sebastian for accompanying me on this project and becoming co-owners (a Microsoft requirement for this type of project).

Leave a comment