PowerShell Script To Enable SCOM Agent Proxy in a More Efficient Way
if you search on how to enable SCOM agent proxy for all your SCOM agents using PowerShell, you’ll get lots of posts and scripts that shows you how to do it in SCOM 2007 or 2012. In fact, I have written few back in the days.
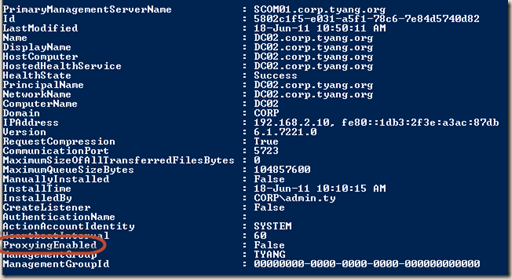
However, no matter if the script uses SCOM 2007 PowerShell Snap-in, or SCOM 2012 PowerShell module, or even SCOM SDK, there is one limitation: the “ProxyingEnabled” property of the agent class is not one of the search criteria that you can use when retrieving the agent:
If you use the SCOM SDK, there are only 4 property names that can be used in the search criteria expression:
- Id
- Name
- LastModified
- DisplayName
So in order to retrieve the agents that are not ProxyingEnabled, we can only client-side filtering, which retrieves ALL agents in the management group and then filter-out the ones that ProxyingEnabled is set to False.
i.e.
Using SCOM 2007 PowerShell Snap-in:
Get-agent | where-object {$_.ProxyingEnabled -match "false"}| foreach {$_.ProxyingEnabled = $true; $_.applyChanges()}
Using SCOM 2012 PowerShell Module:
Get-SCOMAgent | where-object {$_.ProxyingEnabled –match "false"} | Enable-SCOMAgentProxy
Using SCOM SDK in PowerShell:
[System.Reflection.Assembly]::LoadWithPartialName("Microsoft.EnterpriseManagement.OperationsManager.Common") | Out-Null
[System.Reflection.Assembly]::LoadWithPartialName("Microsoft.EnterpriseManagement.OperationsManager") | Out-Null
$RMS = "RMS SERVER NAME"
$MGConnSetting = New-Object Microsoft.EnterpriseManagement.ManagementGroupConnectionSettings(RMS )
$MG = New-Object Microsoft.EnterpriseManagement.ManagementGroup($MGConnSetting)
#Get MG Admin
$Admin = $MG.GetAdministration()
#Search agents
$Agents = $Admin.GetAllAgentManagedComputers()
Foreach ($Agent in $Agents)
{
If (!($Agent.ProxyingEnabled.Value))
{
Write-Host "Enabling Agent Proxy for $($Agent.Name)`..."
$Agent.ProxyingEnabled = $true
$Agent.ApplyChanges()
}
}
Imagine in a large management group with few thousands agents or more and there are only couple of agents that don’t have Agent Proxy enabled. the script / cmdlet will take a long time and a lot of system resources to run because it needs to retrieve information of ALL agents first!
So I wrote a PowerShell script to perform this task a bit differently:
- Firstly run a SQL query against SCOM operational database to retrieve a list of agents that do not have agent proxy enabled
- connect to SCOM SDK and for each agent retrieved from the database, turn on agent proxy.
This is much more efficient as it only retrieves agents that do not have agent proxy enabled, not the whole lot!
The script uses SCOM SDK, it works on both 2007 and 2012 environments.
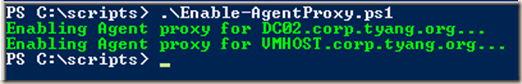
Syntax:
To run it on a SCOM management server, no other parameters need to be specified.
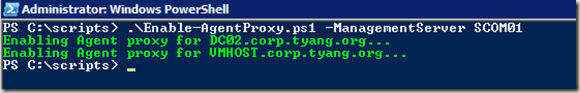
To run it on a SCOM agent, you will need to specify a management server in the management group that you wish to connect to (does not have to be RMS or RMSE)
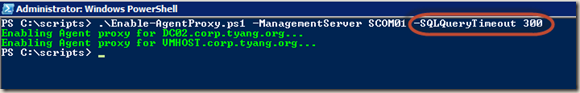
Additionally, the default SQL query timeout is set to 120 seconds, you can specify a different value by using the –SQLQueryTimeout parameter
DOWNLOAD Enable-AgentProxy.ps1
By the way, I also tried to run below SQL command to directly change the ProxyingEnabled attribute in the database (similar to Kevin Holman’s query to change all agents to remote manageable):
Update MT_HealthService Set ProxyingEnabled = 1 where ProxyingEnabled = 0
After I ran this SQL command, the agent proxy setting did get updated in the SCOM console, but I’m not sure if this is supported or not, thus I wrote this script instead.

Leave a comment